What Is The Resource Used For Service Discovery
Editor – This seven‑role series of articles is now complete:
Y'all tin also download the complete ready of manufactures, plus data about implementing microservices using NGINX Plus, every bit an ebook – Microservices: From Pattern to Deployment. Also, delight look at the new Microservices Solutions page.
This is the fourth article in our series about building applications with microservices. The offset article introduces the Microservices Compages pattern and discussed the benefits and drawbacks of using microservices. The second and third articles in the series describe dissimilar aspects of communication within a microservices architecture . In this commodity, we explore the closely related problem of service discovery.
Why Apply Service Discovery?
Let'south imagine that you are writing some code that invokes a service that has a Residue API or Thrift API. In guild to brand a asking, your lawmaking needs to know the network location (IP address and port) of a service case. In a traditional awarding running on concrete hardware, the network locations of service instances are relatively static. For example, your code can read the network locations from a configuration file that is occasionally updated.
In a modern, cloud‑based microservices application, nevertheless, this is a much more than difficult problem to solve every bit shown in the following diagram.
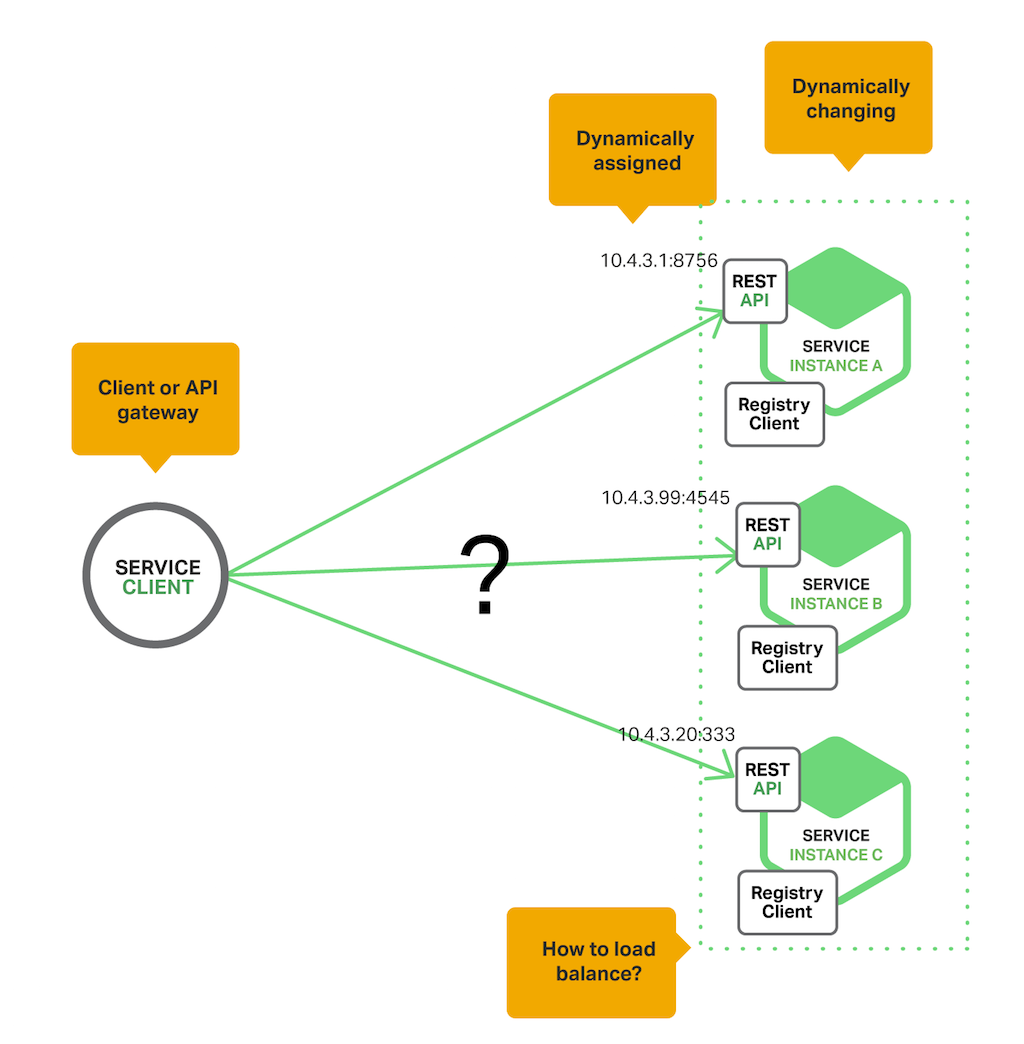
Service instances have dynamically assigned network locations. Moreover, the ready of service instances changes dynamically because of autoscaling, failures, and upgrades. Consequently, your client code needs to use a more elaborate service discovery mechanism.
In that location are two main service discovery patterns: customer‑side discovery and server‑side discovery. Let's first look at client‑side discovery.
The Client‑Side Discovery Blueprint
When using client‑side discovery, the client is responsible for determining the network locations of available service instances and load balancing requests across them. The customer queries a service registry, which is a database of bachelor service instances. The client then uses a load‑balancing algorithm to select one of the available service instances and makes a request.
The post-obit diagram shows the structure of this pattern.
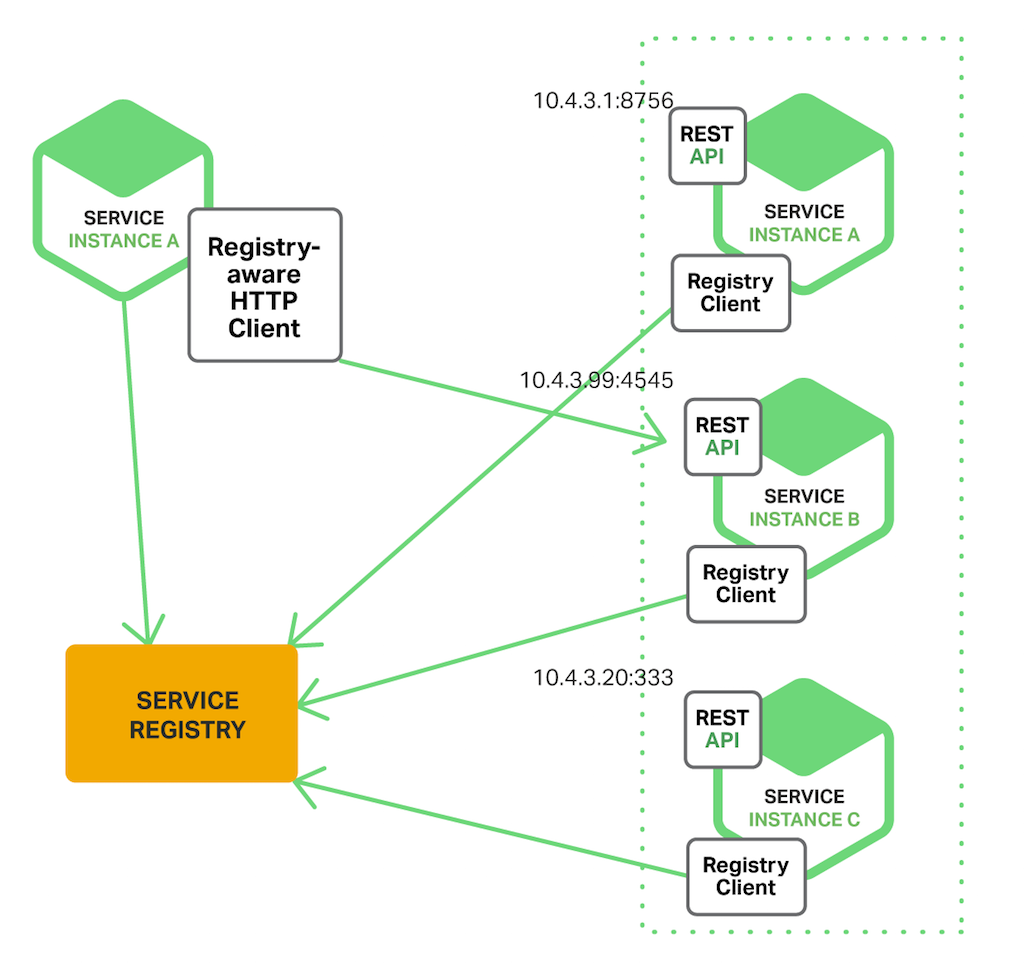
The network location of a service instance is registered with the service registry when information technology starts upwards. It is removed from the service registry when the instance terminates. The service instance'south registration is typically refreshed periodically using a heartbeat machinery.
Netflix OSS provides a great case of the customer‑side discovery blueprint. Netflix Eureka is a service registry. It provides a REST API for managing service‑instance registration and for querying available instances. Netflix Ribbon is an IPC client that works with Eureka to load balance requests beyond the available service instances. We will discuss Eureka in more depth later in this article.
The client‑side discovery blueprint has a variety of benefits and drawbacks. This pattern is relatively straightforward and, except for the service registry, there are no other moving parts. Besides, since the customer knows about the bachelor services instances, it can make intelligent, application‑specific load‑balancing decisions such as using hashing consistently. One pregnant drawback of this pattern is that it couples the client with the service registry. You must implement client‑side service discovery logic for each programming language and framework used past your service clients.
Now that we have looked at customer‑side discovery, allow'southward take a expect at server‑side discovery.
The Server‑Side Discovery Pattern
The other approach to service discovery is the server-side discovery pattern. The following diagram shows the construction of this pattern.

The customer makes a asking to a service via a load balancer. The load balancer queries the service registry and routes each asking to an available service instance. As with client‑side discovery, service instances are registered and deregistered with the service registry.
The AWS Elastic Load Balancer (ELB) is an example of a server-side discovery router. An ELB is commonly used to load balance external traffic from the Net. All the same, you can likewise apply an ELB to load balance traffic that is internal to a virtual individual cloud (VPC). A client makes requests (HTTP or TCP) via the ELB using its DNS proper noun. The ELB load balances the traffic amongst a set of registered Elastic Compute Cloud (EC2) instances or EC2 Container Service (ECS) containers. There isn't a split up service registry. Instead, EC2 instances and ECS containers are registered with the ELB itself.
HTTP servers and load balancers such as NGINX Plus and NGINX can also be used as a server-side discovery load balancer. For example, this blog post describes using Delegate Template to dynamically reconfigure NGINX reverse proxying. Consul Template is a tool that periodically regenerates arbitrary configuration files from configuration information stored in the Consul service registry. It runs an arbitrary shell command whenever the files alter. In the example described past the web log post, Consul Template generates an nginx.conf file, which configures the reverse proxying, and then runs a control that tells NGINX to reload the configuration. A more than sophisticated implementation could dynamically reconfigure NGINX Plus using either its HTTP API or DNS.
Some deployment environments such as Kubernetes and Marathon run a proxy on each host in the cluster. The proxy plays the role of a server‑side discovery load balancer. In club to make a request to a service, a client routes the asking via the proxy using the host's IP address and the service'southward assigned port. The proxy and then transparently frontward the request to an available service instance running somewhere in the cluster.
The server‑side discovery design has several benefits and drawbacks. One swell benefit of this blueprint is that details of discovery are abstracted away from the client. Clients just brand requests to the load balancer. This eliminates the need to implement discovery logic for each programming linguistic communication and framework used by your service clients. Also, as mentioned higher up, some deployment environments provide this functionality for free. This blueprint also has some drawbacks, nevertheless. Unless the load balancer is provided by the deployment environment, it is nonetheless some other highly available system component that yous need to set up and manage.
The Service Registry
The service registry is a primal role of service discovery. It is a database containing the network locations of service instances. A service registry needs to be highly available and up to date. Clients can enshroud network locations obtained from the service registry. Yet, that information eventually becomes out of date and clients get unable to discover service instances. Consequently, a service registry consists of a cluster of servers that employ a replication protocol to maintain consistency.
Every bit mentioned earlier, Netflix Eureka is good example of a service registry. It provides a REST API for registering and querying service instances. A service instance registers its network location using a Postal service request. Every 30 seconds it must refresh its registration using a PUT request. A registration is removed by either using an HTTP DELETE request or by the example registration timing out. As yous might expect, a client tin recall the registered service instances by using an HTTP GET asking.
Netflix achieves loftier availability past running 1 or more Eureka servers in each Amazon EC2 availability zone. Each Eureka server runs on an EC2 instance that has an Elastic IP address. DNS TEXT records are used to store the Eureka cluster configuration, which is a map from availability zones to a list of the network locations of Eureka servers. When a Eureka server starts upwards, information technology queries DNS to retrieve the Eureka cluster configuration, locates its peers, and assigns itself an unused Rubberband IP accost.
Eureka clients – services and service clients – query DNS to discover the network locations of Eureka servers. Clients prefer to utilise a Eureka server in the same availability zone. However, if none is available, the customer uses a Eureka server in another availability zone.
Other examples of service registries include:
- etcd – A highly available, distributed, consequent, key‑value store that is used for shared configuration and service discovery. Two notable projects that use etcd are Kubernetes and Cloud Foundry.
- consul – A tool for discovering and configuring services. Information technology provides an API that allows clients to register and discover services. Consul tin perform health checks to decide service availability.
- Apache Zookeeper – A widely used, loftier‑performance coordination service for distributed applications. Apache Zookeeper was originally a subproject of Hadoop just is now a top‑level projection.
Likewise, as noted previously, some systems such as Kubernetes, Marathon, and AWS do not have an explicit service registry. Instead, the service registry is just a built‑in office of the infrastructure.
Now that we have looked at the concept of a service registry, let'southward expect at how service instances are registered with the service registry.
Service Registration Options
As previously mentioned, service instances must be registered with and deregistered from the service registry. In that location are a couple of different ways to handle the registration and deregistration. I selection is for service instances to annals themselves, the self‑registration pattern. The other option is for some other system component to manage the registration of service instances, the third‑party registration design. Allow's outset expect at the self‑registration pattern.
The Cocky‑Registration Blueprint
When using the self‑registration blueprint, a service instance is responsible for registering and deregistering itself with the service registry. Also, if required, a service example sends heartbeat requests to preclude its registration from expiring. The post-obit diagram shows the construction of this design.
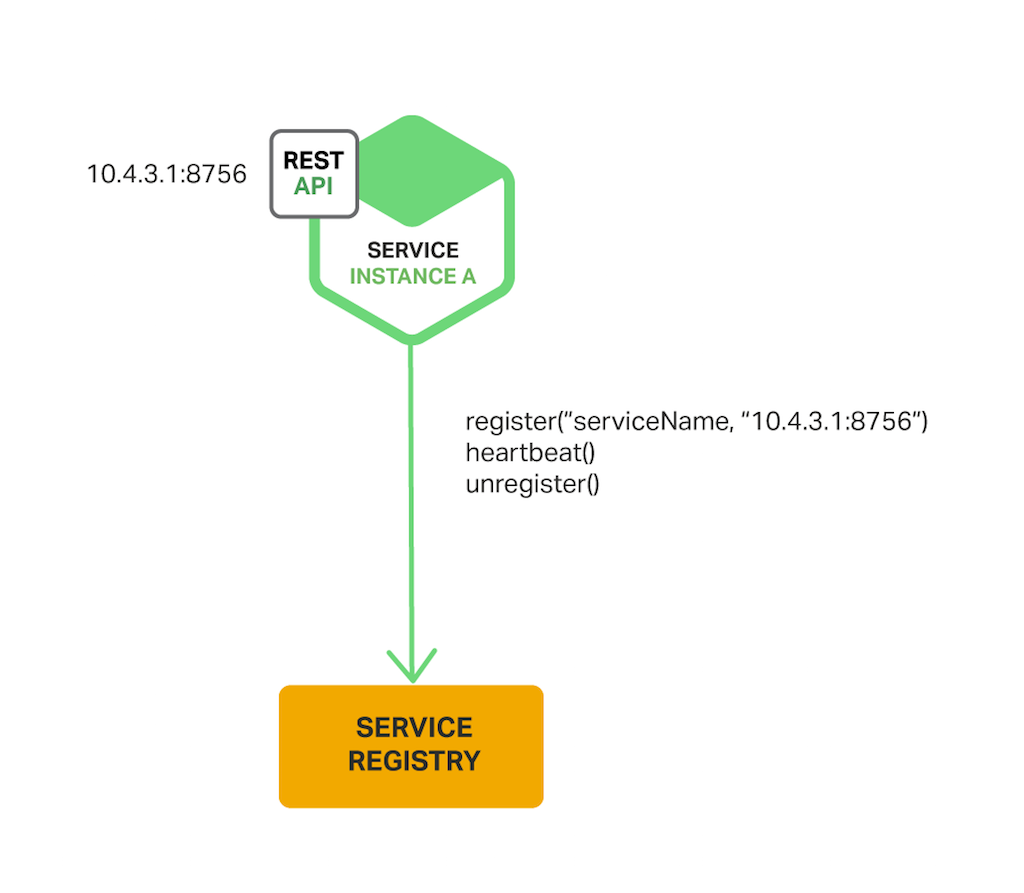
A adept example of this arroyo is the Netflix OSS Eureka client. The Eureka client handles all aspects of service instance registration and deregistration. The Leap Cloud project, which implements diverse patterns including service discovery, makes it easy to automatically register a service instance with Eureka. You just annotate your Java Configuration class with an @EnableEurekaClient annotation.
The self‑registration pattern has various benefits and drawbacks. One benefit is that it is relatively simple and doesn't require any other system components. However, a major drawback is that it couples the service instances to the service registry. You must implement the registration lawmaking in each programming language and framework used by your services.
The alternative approach, which decouples services from the service registry, is the 3rd‑political party registration pattern.
The Tertiary‑Party Registration Blueprint
When using the 3rd-party registration pattern, service instances aren't responsible for registering themselves with the service registry. Instead, some other organization component known as the service registrar handles the registration. The service registrar tracks changes to the set of running instances by either polling the deployment environment or subscribing to events. When it notices a newly available service instance it registers the case with the service registry. The service registrar also deregisters terminated service instances. The post-obit diagram shows the structure of this pattern.
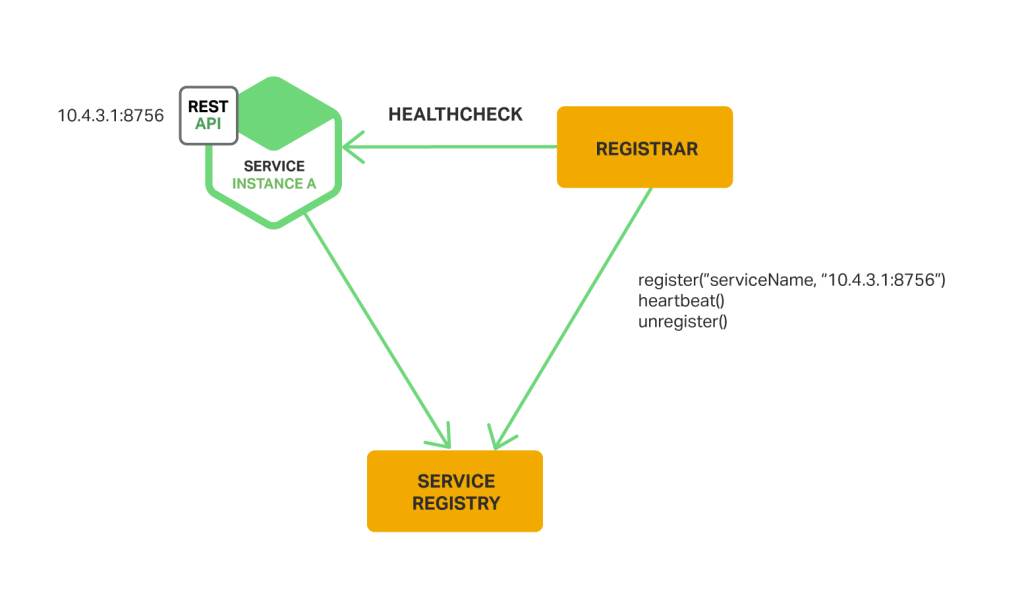
I example of a service registrar is the open source Registrator project. Information technology automatically registers and deregisters service instances that are deployed equally Docker containers. Registrator supports several service registries, including etcd and Consul.
Another example of a service registrar is NetflixOSS Prana. Primarily intended for services written in non‑JVM languages, information technology is a sidecar application that runs next with a service instance. Prana registers and deregisters the service instance with Netflix Eureka.
The service registrar is a built‑in component of deployment environments. The EC2 instances created by an Autoscaling Group can exist automatically registered with an ELB. Kubernetes services are automatically registered and made available for discovery.
The third‑party registration pattern has various benefits and drawbacks. A major benefit is that services are decoupled from the service registry. You don't demand to implement service‑registration logic for each programming linguistic communication and framework used by your developers. Instead, service case registration is handled in a centralized fashion within a dedicated service.
Ane drawback of this design is that unless information technology's built into the deployment environment, it is all the same another highly bachelor organization component that you need to set and manage.
Summary
In a microservices awarding, the set of running service instances changes dynamically. Instances have dynamically assigned network locations. Consequently, in guild for a client to brand a request to a service it must use a service‑discovery mechanism.
A central office of service discovery is the service registry. The service registry is a database of bachelor service instances. The service registry provides a direction API and a query API. Service instances are registered with and deregistered from the service registry using the direction API. The query API is used by system components to discover available service instances.
There are two main service‑discovery patterns: client-side discovery and service-side discovery. In systems that utilize client‑side service discovery, clients query the service registry, select an available instance, and brand a request. In systems that use server‑side discovery, clients brand requests via a router, which queries the service registry and forwards the asking to an available instance.
At that place are 2 main ways that service instances are registered with and deregistered from the service registry. One option is for service instances to annals themselves with the service registry, the self‑registration pattern. The other option is for another arrangement component to handle the registration and deregistration on behalf of the service, the tertiary‑party registration blueprint.
In some deployment environments y'all need to set your ain service‑discovery infrastructure using a service registry such as Netflix Eureka, etcd, or Apache Zookeeper. In other deployment environments, service discovery is congenital in. For instance, Kubernetes and Marathon handle service instance registration and deregistration. They also run a proxy on each cluster host that plays the office of server‑side discovery router.
An HTTP opposite proxy and load balancer such as NGINX tin also be used as a server‑side discovery load balancer. The service registry can push the routing information to NGINX and invoke a graceful configuration update; for example, you lot tin use Delegate Template. NGINX Plus supports additional dynamic reconfiguration mechanisms – it can pull data most service instances from the registry using DNS, and it provides an API for remote reconfiguration.
In future blog posts, we'll continue to dive into other aspects of microservices. Sign up to the NGINX mailing list (form is below) to be notified of the release of future articles in the series.
Editor – This seven‑role series of articles is now complete:
You lot can too download the complete fix of manufactures, plus information near implementing microservices using NGINX Plus, as an ebook – Microservices: From Blueprint to Deployment.
Invitee blogger Chris Richardson is the founder of the original CloudFoundry.com, an early on Java PaaS (Platform as a Service) for Amazon EC2. He now consults with organizations to improve how they develop and deploy applications. He also blogs regularly about microservices at https://microservices.io.
What Is The Resource Used For Service Discovery,
Source: https://www.nginx.com/blog/service-discovery-in-a-microservices-architecture/
Posted by: hickstung1962.blogspot.com


0 Response to "What Is The Resource Used For Service Discovery"
Post a Comment